- cross-posted to:
- [email protected]
- cross-posted to:
- [email protected]
I’d avoid anything related to Cake Wallet (e.g. its remote nodes), seeing that the OP sgp = SamsungGalaxyPlayer is doing this side business—chain analysis, offering suspicious activity reports for CEXes, ready to collaborate with law enforcement if paid.
In 2022, it was noticed that someone from Team Cymru, a company trading net flow data, was a board member of the Tor Project, providing bandwidth, hardware, bridges (entry points to the Tor network). There was a fix: Remove Team Cymru hard-coded bridges.
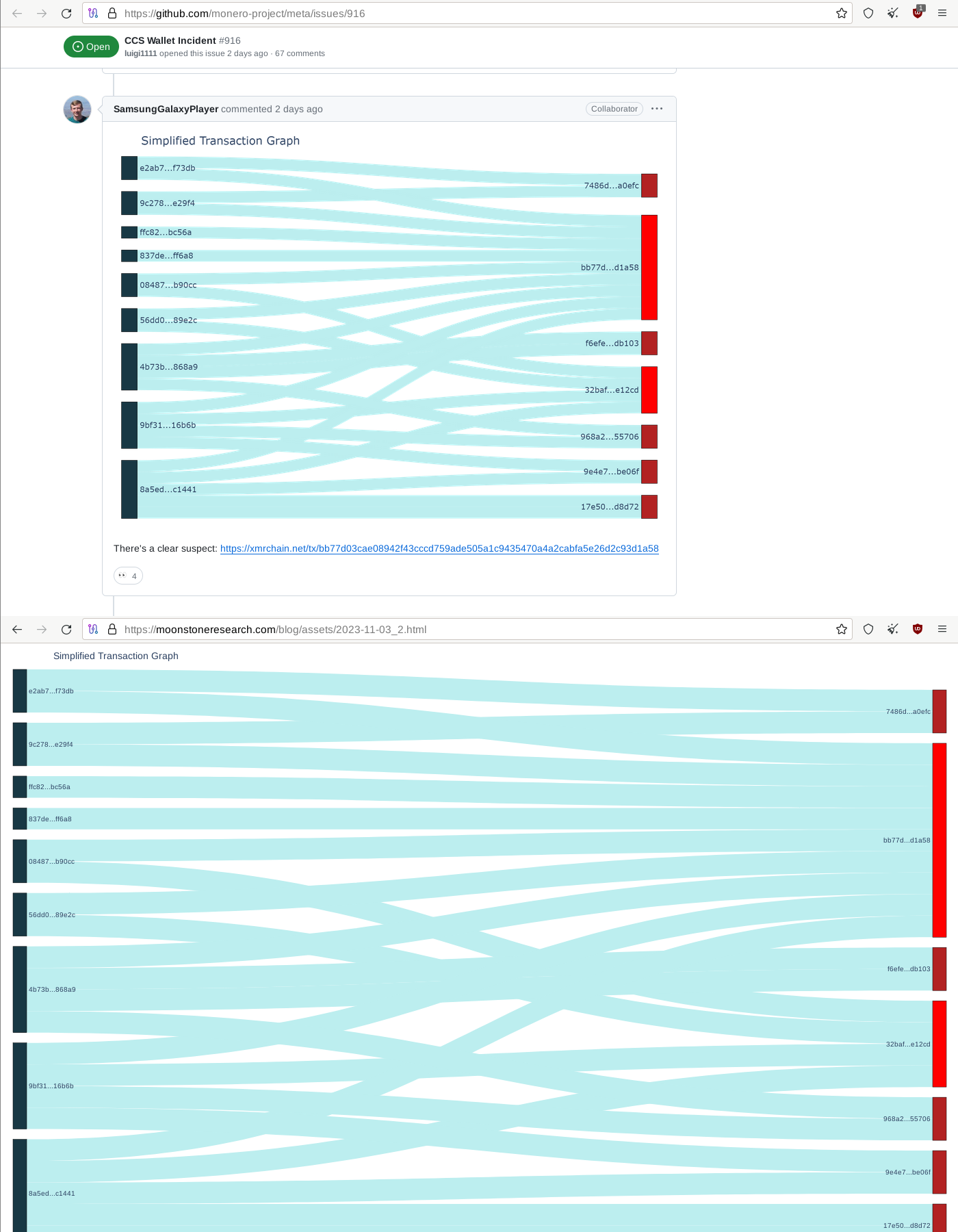
Now “Moonstone Research” is proudly saying they can trace things that other companies can’t, and they’re related to Cake Wallet directly or at least indirectly, or so it seems.
This possible suspicion aside, the analysis itself is interesting. While it might be good news if we can identify the attacker, that would be actually very bad news for Monero!
I’m thankful that this research organization is making these publications public. If the data is there, and it can be analyzed, it’s good that we’re aware of it. Our threat model should be based on capabilities, and demonstrating a capability is valuable.
I want to thank SGP for posting this.
My thought exactly, when I first read it. Still, just in case, I’d avoid using remote nodes related to Cake Wallet. It might be “honey pot flavored” cake, haha, although I’d like to believe that’s not true. Come to think of it, the monero.com domain must have been really expensive.
if we can identify the attacker, that would be actually very bad news for Monero!
Yes and no - Monero is well on the way to transitioning to the (nearly) full chain Decoy Selection range WIP
True. And no one even knows (yet) what was the problem to begin with.
Moonstone Research Study Etches Doubts on Monero’s Privacy; Crypto Community Reacts
Moonstone’s investigation demonstrates, under certain circumstances, XMR transactions can sometimes be partially traced despite their privacy features. […] “Wow… not as private as everyone thinks,” one person remarked.
Simmons shared his perspective about Moonstone’s study as well and stressed that the specific tracing scenario doesn’t apply to the typical Monero user. […] He explained that the ability to trace resulted from unusual circumstances: private keys were shared with a chain surveillance company.
Identifying the pocket change transaction is really interesting.
One big talking point in monero, is fungible coins. No tainted coins. But it is interesting that this research firm has a tainted transaction, that they’re encouraging exchanges to look for.
Right? On one hand it’s awful the CCS fund was stolen and I hope they catch whoever did it. However, if they’re caught using huristics of their transactions then it’s a bow against the fungiablity of Monero.
Luckily there are contributors out there still helping to iterate monero instead of forking to make a new version and claiming they are the creator.
Is that a dig at signals mobile coin?
Or ETC