- cross-posted to:
- [email protected]
- cross-posted to:
- [email protected]
cross-posted from: https://lemmy.world/post/2852886
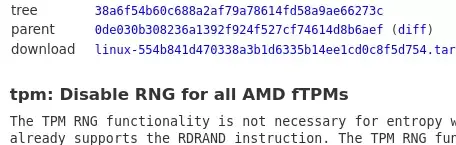
For those out of the loop, some AMD users have been suffering from stuttering issues caused by the AMD fTPM random number generator. A firmware/BIOS update appears to fix the issue for some users, but not others, leading to more bug reports being sent in. Last week, Linus Torvalds said “let’s just disable the stupid fTPM hwrnd thing”, and, as of today the Linux kernel has gone ahead and blanket disabled RNG use for all current AMD fTPMs.


Well Linux is using rdrand in place of the fTPM one so … from firmware to hardware. Then again even if you generate random numbers using pure software, is your CPU or firmware FOSS and without bugs (cough … Debian OpenSSL maintainers, cough) or exploits (Ken Thompson says hi)? If not, and you assume you can’t trust the firmware and hardware - all your random numbers are belong to us. Gotta draw the line somewhere, unless you’re building your machine from diodes and solder. Personally, I live in a Five Eyes country so I’m alright using the hardware the NSA/GCHQ/CSIS/etc use. If I’m fucked, they’re fucked.
Relevant meme.
That depends on your distribution’s setting of the CONFIG_RANDOM_TRUST_CPU compile-time configuration option and the random.trust_cpu sysctl setting. I’m not sure what the major distributions are doing with that at the moment.
Like you said, it is impossible to be completely safe. But using proprietary cryptographic hardware/firmware, the inner workings of which are known only to Intel, introduces a lot of risk. Especially when we know the NSA spends hundreds of millions of dollars on bribing companies to introduce backdoors into their products. At least when it’s an open source cryptographic library they have to go to great lengths to create subtle bugs or broken algorithms that no one notices.
Our CPUs are certainly backdoored too, beyond RDRAND. But it’s way more complicated to compromise any arbitrary cryptographic algorithm running on the CPU with a backdoor than making a flawed hardware RNG. Any individual operation making up a cryptographic algorithm can be verified to have executed properly according to the specification of the instruction set. It would be very obvious, for example, if XORing two 0s produced a 1, that something is very wrong. So a backdoor like this would have to only activate in very specific circumstances and it would be very obvious, limiting its use to specific targets. But a black box that produces random numbers is very, very difficult to verify.
Ultimately, the real solution is the dissolution of the American security state and the computer monopolies.
Not if they’re the only ones who know about the backdoors.
Edit: I started writing that before your edit about the “Ken Thompson hack”. An element of any good backdoor would include obfuscation of its existence, of course. The issue is it is impossible to predict every possible permutation of operations that would result in discovery of the backdoor and account for them. Maybe if you had a sentient AI dynamically rewriting its own code… anyway, backdoors in tooling like compilers is very concerning. But I’m not too concerned about a Ken Thompson type attack there just because of how widely they’re used, how many different environments they run in, and how scrutinized the outputted code is.